Transaction Attestation
Cryptographic proof attached to every financial transaction, providing immutable evidence of execution and compliance state.
For environments where AI outputs must become verifiable records — machine credentials, asset passports, compliance artifacts that travel across institutions.
Attach cryptographic evidence to every transaction, attestation, and regulatory report. Aethelred supports tokenized financial infrastructure when needed, but leads with auditable records, policy-aware asset identity, and proof-backed settlement.

Cryptographic proof attached to every financial transaction, providing immutable evidence of execution and compliance state.
Verifiable audit trails for regulatory submissions, ensuring every report is backed by attestable evidence from source to filing.
Deterministic finality for international transactions with proof-backed settlement across jurisdictions and counterparties.
Produce verifiable clinical records, research outputs, and data-handling evidence for protected workflows. Aethelred protects sensitive operations without exposing underlying data.
Verifiable records of AI-assisted clinical decisions, preserving evidence chains from model inference to patient outcome.
Cryptographic attestation for research methodologies, datasets, and results, ensuring reproducibility and trust in published findings.
Proof-backed audit trails for sensitive data workflows, demonstrating compliance without exposing protected health information.
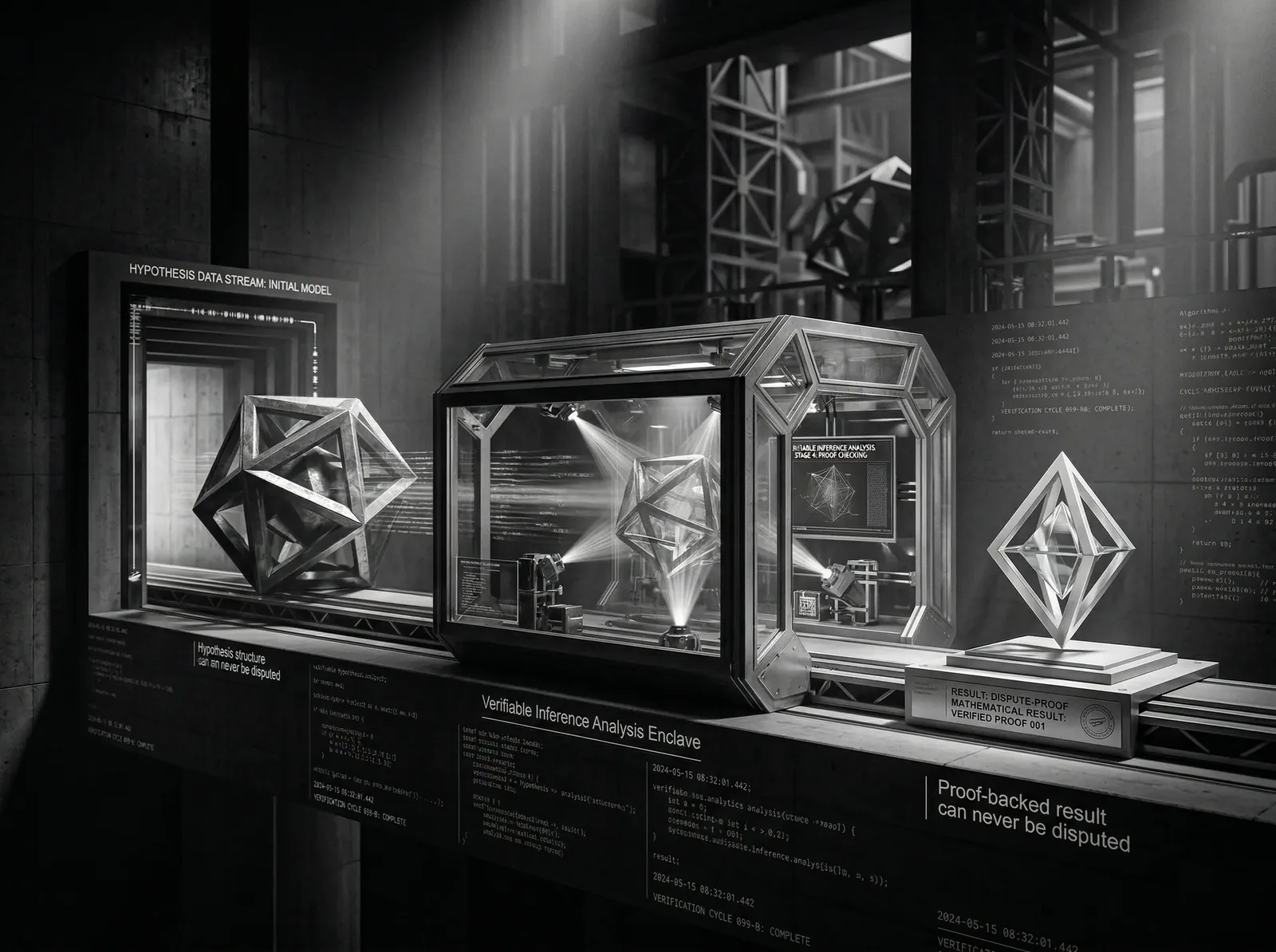
Execution evidence, attested inference, and sovereign-grade security for national infrastructure, defense intelligence, and critical government operations.

Hardware-attested proof of computation for mission-critical operations, ensuring every decision is backed by verifiable execution records.
National-grade compute infrastructure with post-quantum security, geographic sovereignty, and full operational independence.
Confidential compute within hardware enclaves for sensitive intelligence and defense operations with attestation at every stage.
Verifiable origin, transfer, and compliance states across global trade networks. Attach cryptographic evidence to every handoff, inspection, customs declaration, and item-level product passport.
Cryptographic product passports bind provenance, inspection, and lifecycle history to each unit, making origin claims verifiable and tamper-evident.
Attested handoff records across every node in the supply chain, providing an unbroken chain of custody from origin to destination.
Verifiable compliance documentation for cross-border trade, with cryptographic evidence attached to every customs declaration and inspection.
Autonomous vehicles, fleet management, and connected transport systems need provable decision-making plus durable records for vehicles, components, and operating corridors. Aethelred provides cryptographic accountability for machine-driven mobility.
Verifiable records of every decision made by autonomous systems, providing cryptographic accountability for machine-driven actions.
Sealed records for maintenance, firmware, safety checks, and component lineage create an auditable digital twin for every vehicle and critical part.
Vehicle-to-everything communication backed by cryptographic verification, establishing trust between vehicles, infrastructure, and networks.
When AI agents transact, negotiate, and make decisions with other AI agents, trust cannot be implicit. Aethelred provides verifiable identity, capability credentials, usage entitlements, and settlement evidence for agent-to-agent systems.

Cryptographic identity and attestation for autonomous agents, ensuring every participant in an agent network is verified and accountable.
Verifiable records of multi-agent decision sequences, providing an auditable trail of negotiations, agreements, and executions.
Proof-backed records for agent-to-agent service usage, tool access, settlement, and dispute resolution keep autonomous commerce accountable.
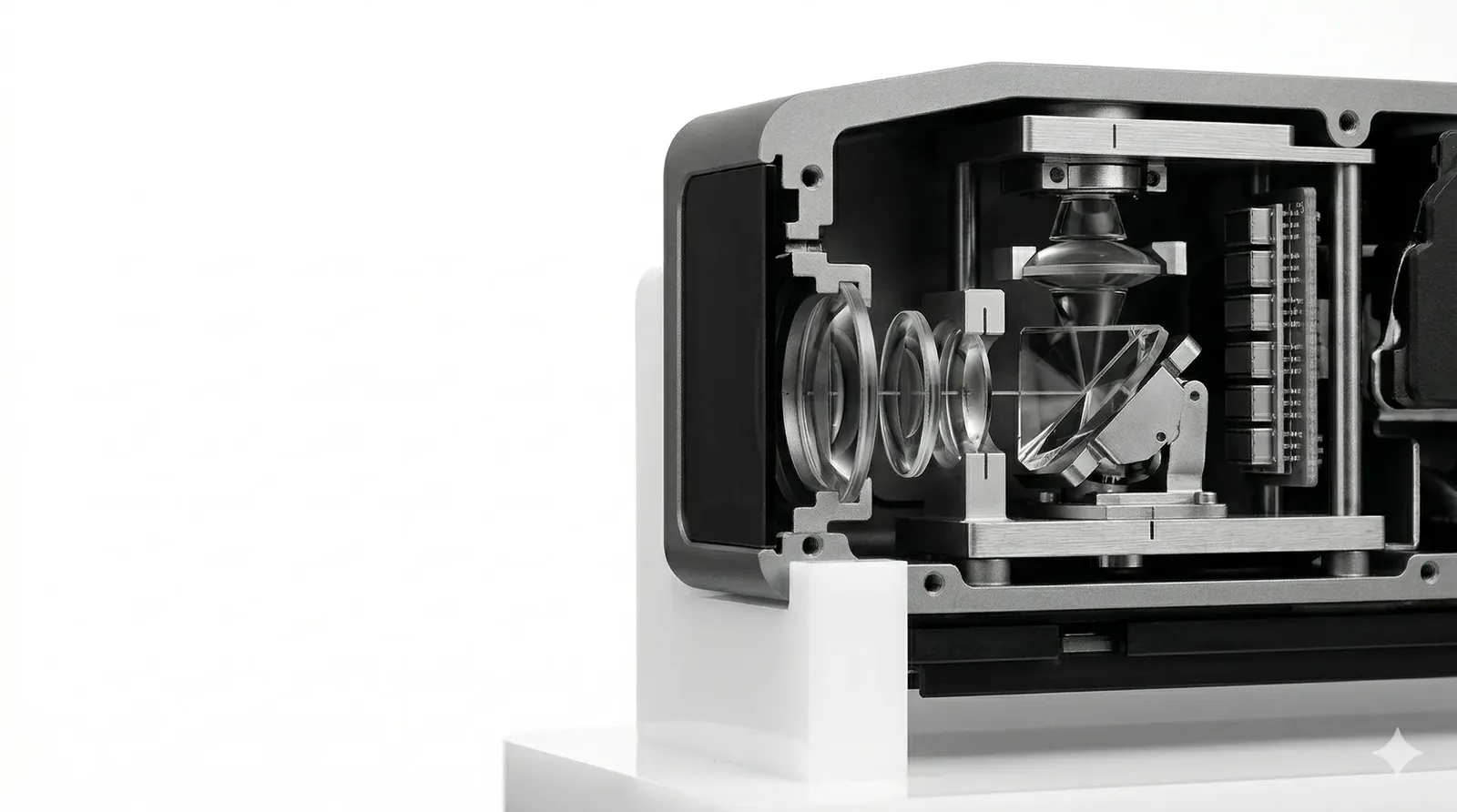
Computational research demands reproducibility, lineage, and licensing clarity. Aethelred attaches execution evidence to every model run, dataset transformation, and published result.
Cryptographic attestation for every experiment, capturing parameters, data inputs, and execution environment with verifiable evidence.
Hardware-attested execution records for model training and inference, ensuring any result can be independently verified and reproduced.
Sealed records for datasets, model artifacts, authorship, and licensing terms make reuse, attribution, and downstream commercialization auditable.
Review the architecture, explore security, and connect with the team.