ML-KEM-768 and ML-DSA-65 from genesis.
Security is not a feature. It is the operating model.
Every inference goes through TEE attestation and a zero-knowledge proof. If either fails, the workload does not settle.
Secure by design, not by patch.
Every layer of the Aethelred protocol is built with security as a primary constraint. From post-quantum cryptography at the signature level to hardware-attested execution at the compute layer, security is structural rather than supplemental.
Intel SGX, AWS Nitro, AMD SEV-SNP enclaves.
TEE attestation plus zero-knowledge proofs per job.
Quantum-resistant from genesis.
Aethelred does not retrofit post-quantum security. ML-DSA-65 (FIPS 204) signatures and ML-KEM-768 (FIPS 203) key exchange are native to the protocol from block zero. There is no migration path because none is needed.
ML-DSA-65 Signatures
Digital signatures based on lattice problems. NIST FIPS 204 standardized. Used for all transaction signing, validator attestation, and governance votes.
ML-KEM-768 Key Exchange
Key encapsulation mechanism for secure channel establishment. NIST FIPS 203 standardized. Used for validator-to-validator communication and enclave key provisioning.
Fail-Closed Design
No classical fallback. If the post-quantum primitive fails, the operation fails. This prevents silent downgrade attacks that compromise quantum resistance.
Hardware-enforced confidentiality.
AI inference runs inside attested hardware enclaves. The host operating system, hypervisor, and co-tenant workloads cannot observe or tamper with computation. Attestation quotes bind each workload to its execution context.
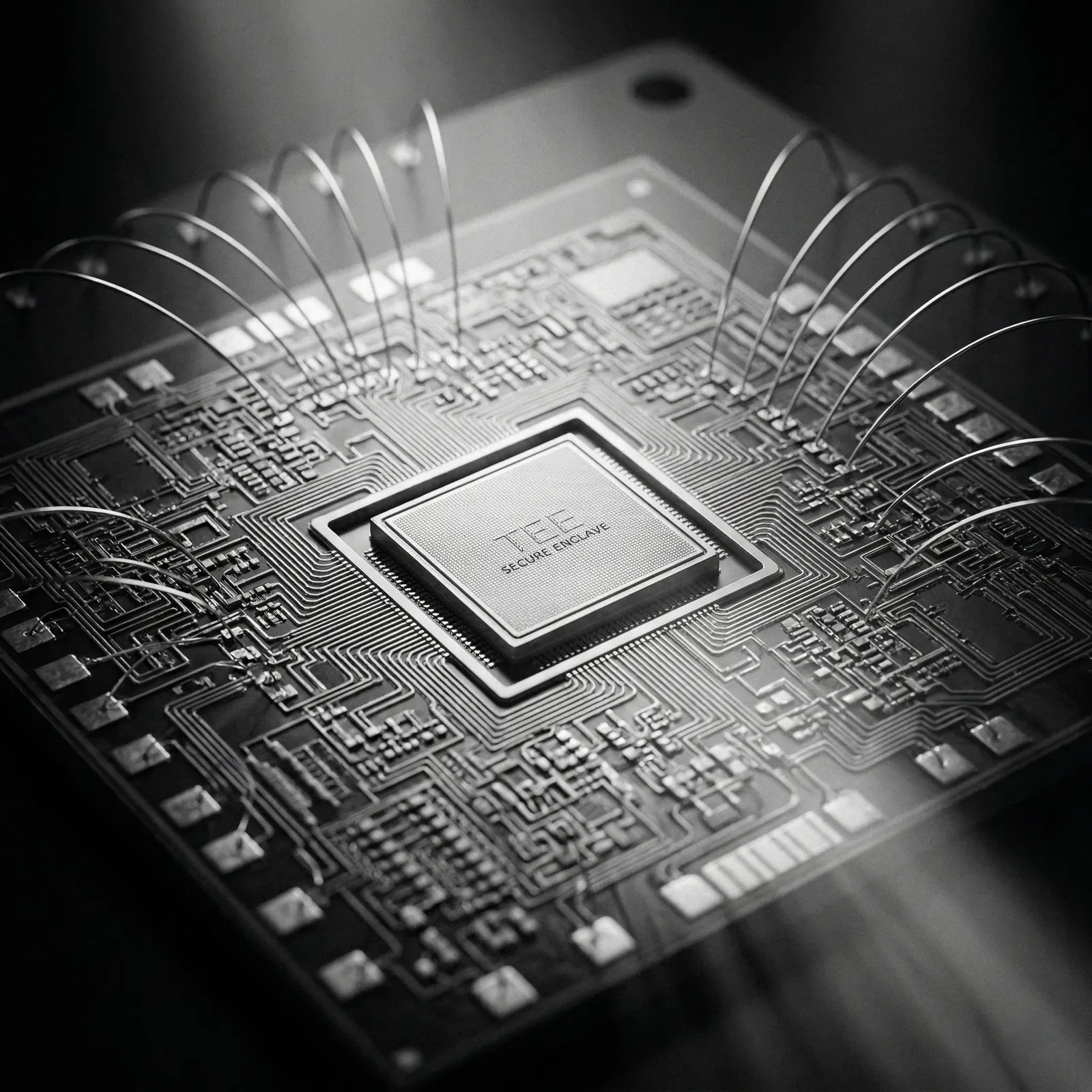
Intel SGX / DCAP
Data Center Attestation Primitives for Intel SGX enclaves. Remote attestation verifiable on-chain without reliance on Intel Attestation Service.
AWS Nitro Enclaves
Isolated compute environments with cryptographic attestation. No persistent storage, no interactive access, no external networking.
AMD SEV-SNP
Secure Encrypted Virtualization with Secure Nested Paging. Memory encryption with integrity protection against hypervisor-level attacks.
Five proof systems. One unified verifier.
Aethelred supports Groth16, PLONK, EZKL, Halo2, and STARK proof systems through EVM precompiles at addresses 0x0300 and 0x0400. Each proof is verified on-chain with deterministic gas costs and cryptographic binding to the settlement layer.
| Proof System | Type | Use Case | Verification Cost |
|---|---|---|---|
| Groth16 | zk-SNARK | General ZKP, small proofs | Lowest gas |
| PLONK | Universal SNARK | Flexible circuits | Moderate gas |
| EZKL | ML-native | Neural network inference proofs | Optimized for ML |
| Halo2 | Recursive | Proof aggregation, batching | Scalable |
| STARK | Transparent | No trusted setup required | Higher gas, trustless |
Byzantine fault tolerance with useful work.
CometBFT consensus with Proof-of-Useful-Work validation. Validators perform real AI inference as part of consensus participation, eliminating wasted computation while maintaining deterministic finality and slashing guarantees.
Deterministic Finality
No probabilistic confirmation. Once a block is committed, it is final. Proof references are anchored with cryptographic binding to block height and validator set.
Slashing & Accountability
Extended downtime, equivocation, and attestation fraud trigger slashing. Validator reliability scores weight governance power and reward distribution.
VRF Job Scheduling
Verifiable Random Function distributes inference jobs across the validator set. Prevents validator collusion and ensures fair workload distribution.
Transparent security practices.
External security audits, continuous benchmark verification, and a structured responsible disclosure program. Aethelred publishes audit reports, maintains a public bug bounty, and operates a dedicated security response team.
External Audits
Independent security audits by recognized firms. Full reports published on completion. Scope covers smart contracts, consensus logic, cryptographic implementations, and TEE integration.
Bug Bounty Program
Structured rewards for responsible disclosure. Critical vulnerabilities receive the highest tier bounties. All submissions reviewed by the security team within 48 hours.
Security Response
Dedicated incident response team with defined escalation procedures. Coordinated disclosure timelines. Post-incident reports published for community transparency.
Bring verifiable intelligence into production.
Explore the architecture, review the security model, and connect with the team building the trust layer for AI-native systems.